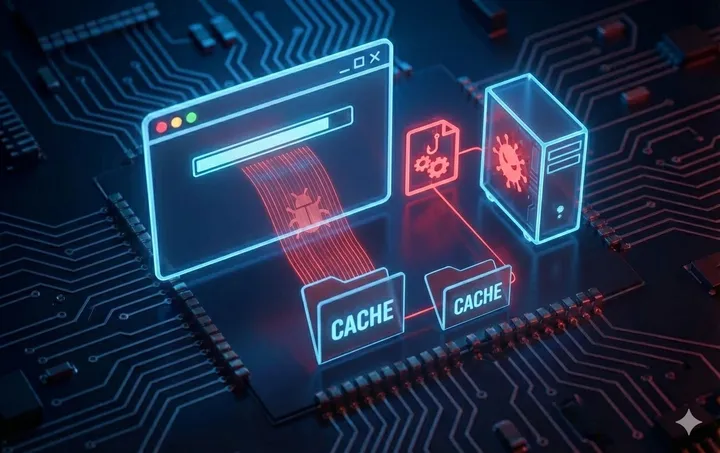
The Malware Was Already There
What if the malware was already on disk before the attack even started? We walk through a technique that abuses browser caching behaviour and Windows COM resolution order to achieve persistence in corporate environments.